Réseaux
Sécurisez le trafic et l’exposition sur internet de vos applications grâce à nos solutions d’interconnexion réseaux et connectivité, de gestion de trafic et d’équilibrage de charge.
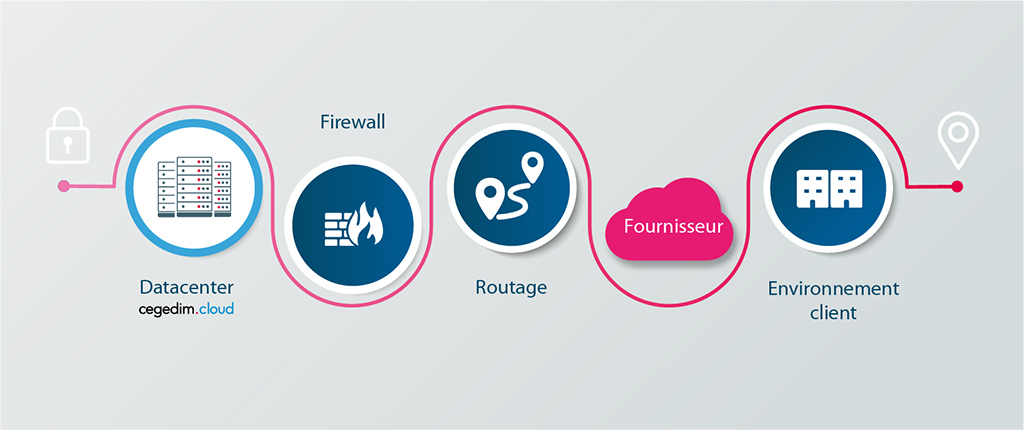
Interconnexions
cegedim.cloud héberge plus de 300 interconnexions clients et assure la mise en place d’une interconnexion sécurisée et privée entre vos environnements et le réseau Cegedim.
Ces différents supports d’interconnexion peuvent être combinés et déployés comme interconnexion principale et/ou interconnexion de secours afin de garantir la haute disponibilité des liens.
Supports managés
- Managed Dedicated Link Interconnection + Service Provider Link : Interconnexion managée au DC par lien physique dédié
- Managed VPN Site to site : Accès VPN Site to Site managé
Support non managés
cegedim.cloud n’intervient pas sur vos équipements – sauf demande client spécifique. Nous garantissons la disponibilité de nos équipements.
- Unmanaged Dedicated Link Interconnection : Interconnexion non managée au DC par lien physique ; le lien opérateur est à la charge du client. Cegedim.cloud met à disposition une interconnexion sécurisée à son réseau par VLAN, charge au client de ramener son équipement hardware.
- Unmanaged VPN site to site : Accès VPN Site to Site non managé
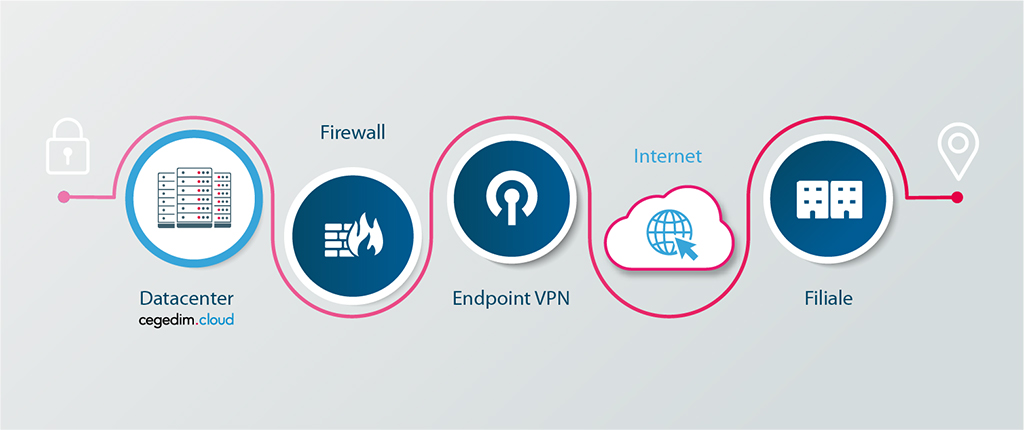
VPN Ipsec utilisateur
La solution VPN Ipsec utilisateur vous permet un accès distant et sécurisé à votre réseau. Vous accédez à l’ensemble de vos ressources depuis n’importe quel lieu distant grâce à un réseau privé, isolé et sécurisé.
VPN Ipsec utilisateur fournit les fonctionnalités suivantes :
- Service managé : le déploiement, la gestion et le maintien en condition opéationnelle de la plateforme sont assurés par nos équipes
- Connexions sécurisées TLS
- Haute disponibilité
- Authentification clients basée sur l’Active Directory
Nom de domaine et certificats
Les certificats permettent de sécuriser vos applications et sites exposés sur internet en assurant le chiffrement des données en transit entre un utilisateur et un site web. Le certificat permet d’établir une connexion sécurisée entre le serveur web et le navigateur. Les visiteurs accèdent alors à votre site à travers une connexion sécurisée indiquée par une icône en forme de cadenas et une URL commençant par le protocole « https ».
cegedim.cloud assure le déploiement et la gestion des certificats SSL/TLS (Secure Sockets Layer/Transport Layer Security), et propose plusieurs types de certificat :
- Standard : émis pour une seule url
- Wildcard : permet de sécuriser un nombre illimité d’urls d’un domaine ou sous-domaine de votre choix
- Multi-Wildcard : nombre illimité d’urls pour plusieurs domaines et sous-domaines sur le même certificat
- Extended Validation : propose le plus haut niveau d’authentification
- Let’s Encrypt : certificats générés par cegedim.cloud et autogérés. Ces certificats sont renouvelables à l’infini.
cegedim.cloud fournit un service managé, de la mise à disposition du nom de domaine à la gestion des certificats SSL/TLS :
- Location de nom de domaine
- Achat des certificats auprès des autorités de certification
- Déploiement et gestion du cycle de vie, notamment renouvellement des certificats
Elastic Secured Endpoint
Exposées sur internet, vos applications sont particulièrement exposées aux risques de cyberattaques : botnets, attaques par déni de service (DDoS), intrusion, fuite de données, etc. cegedim.cloud fournit ainsi à travers le service Elastic Secured Endpoint, un ensemble complet de technologies permettant l’exposition sécurisée de vos applications sur internet.
Elastic Secured Endpoint est un service entièrement managé par notre équipe d’experts en sécurité qui assure le déploiement, la gestion et le reporting de la solution :
- Sécurité et Performance de vos applications :
- Chiffrement/déchiffrement des flux HTTPS
- Gestion intelligente du trafic et répartition de charge
- Gestion de la compression et du cache pour une performance maximale
- Pare-feu applicatif web (WAF) en option
- Surveillance Sécurité :
- Cyber Surveillance en temps réel de vos ressources exposées sur Internet
- Audits de vulnérabilités hebdomadaires
- Protection DDoS :
- Détection et protection contre les attaques par déni de service
Sécurité et performance des applications
Les répartisseurs de charge cegedim.cloud (F5 BIG-IP LTM) apporte une compréhension profonde du trafic applicatif du réseau et le contrôle sur la façon dont il est géré.
Il transforme le volume chaotique du trafic du réseau en flux de données logiquement assemblés, puis prend des décisions de gestion du trafic intelligentes, en sélectionnant la bonne destination en fonction des performances du serveur, de la sécurité et de la disponibilité.
BIG-IP LTM est un reverse proxy complet permettant d’inspecter, gérer et constituer des rapports sur le trafic applicatif de votre réseau. De l’équilibrage de charge de base à des décisions de gestion du trafic complexes basées sur le client, le serveur ou l’état de l’application, BIG-IP LTM vous procure un contrôle très précis sur le trafic applicatif.
L’accélération SSL réalisée par le BIG-IP LTM permet de décharger les serveurs du chiffrement des flux HTTPS et libère des ressources pour améliorer la performance applicative.
La gestion optimisée de la compression et de la mise en cache améliore les performances des applications interactives, les temps de chargement des données et l’utilisation de la bande passante.
- Optimisation de la vitesse et de la fiabilité des applications
- Amélioration des performances des infrastructures
- Optimisation de l’expérience utilisateur
Caractéristiques :
Décision intelligente de gestion de trafic en fonction des applications et des contraintes serveur
Flexibilité (évolutivité des ressources à la demande)
Analyses en temps réel (continuité, temps de réponse, augmentation de trafic, etc.)
Chiffrement du trafic
TCP/IP optimisé
Déchargement SSL
Web Application Firewall (F5 BIG-IP ASM)
La gestion de sécurité applicative BIG-IP (ASM) permet aux organisations de se protéger contre les 10 plus grandes menaces selon l’OWASP, les vulnérabilités des applications et les attaques Zero-day. L’association de défenses DDoS de la couche 7, de techniques avancées de détection et de réduction, d’un apprentissage dynamique, d’une exécution virtuelle du correctif et d’une visibilité précise des attaques repousse même les menaces les plus complexes avant qu’elles n’atteignent vos serveurs.
Avantages :
La sécurité prête à l'emploi la plus efficace
- BIG-IP ASM simplifie la création de politiques, vous permettant ainsi de déployer rapidement un WAF et d’assurer une puissante sécurité immédiatement. Il adapte également les politiques grâce à l’apprentissage automatique, pour contrer les menaces en évolution constante se cachant dans (ou ciblant) les trafics http, https et WebSocket.
Visibilité d'applications détaillée et rapports
- Obtenez une visibilité détaillée en matière de violations de politiques, gravité potentielle d’attaque et impact sur les serveurs. BIG-IP ASM utilise également les informations et rapports d’attaques pour identifier les menaces, de plus en plus sophistiquées à mesure qu’elles évoluent.
Correction rapide de la vulnérabilité
- BIG-IP ASM intègre des outils de test de sécurité applicative dynamique tiers (DAST) pour détecter et corriger les vulnérabilités et les modifications web non autorisées avant que les corrections de codes ne soient disponibles.
La performance et l'évolutivité leaders sur le marché
- Garantir la disponibilité des applications, même en cas d’attaque, et améliorer les performances de façon dynamique, grâce à l’optimisation et l’accélération applicatives.
Fonctionnalités :
Protection contre les attaques de la couche 7
- Détecte et réduit les attaques d’applications, notamment les attaques DOS et DDOS, de force brute, d’injection SQL, de script intersites, d’insertion de fichier à distance, d’empoisonnement de cookie et de détournement de session.
Identification de l’équipement
- Elle suit l’ID du périphérique unique de chaque visiteur sur plusieurs IP et sessions et par des actions d’évitement, pour une grande précision du blocage des acteurs malveillants.
Défense proactive contre les robots
- Elle identifie les robots malveillants qui outrepassent les méthodes de détection standards et réduit les menaces avec une plus grande précision, avant qu’elles ne commencent.
Perception des applications
- En associant le nom d’utilisateur de l’application aux attaques, BIG-IP ASM permet de bloquer la quasi-totalité des attaques et de mieux les comprendre.
Protection des données et « Cloaking » (anonymisation des données)
- Empêchez les fuites de données sensibles (informations de cartes de crédit, numéros de sécurité sociale) en éliminant complètement les données et en masquant les informations.
Groupement d'incidents et corrélation des attaques
- Mettez automatiquement en correspondance plusieurs attaques en un seul incident pour améliorer la visibilité et faciliter la gestion.
Cybersurveillance des ressources exposées
XMCO est un service non intrusif de détection de tentatives d’attaques et de fuite d’informations sensibles. Le service couvre l’ensemble des ressources associées à l’entreprise : adresses IP, domaines, marques, noms, et détecte les vulnérabilités de façon préventive, avant qu’elles ne soient exploitées par les pirates : atteinte à l’image, usurpation d’identité, préparation d’une attaque, exposition non maitrisée du SI, vols et fuites de données, etc.
- Détection des menaces et anticipation des attaques :
- Exposition soudaine d’un service ou d’une interface d’administration
- Exposition vis-à-vis d’une faille exploitable (Heartbleed, Wannacry, Struts…)
- Compromission d’un site
- Erreurs de configuration
- Référencement des adresses IP sur listes noires
- Exposition de dossiers ou fichiers dangereux au sein d’applications web
- Exhaustivité des périmètres surveillés :
- Périmètres « maîtrisés » (sites web, infrastructure IP, domaines)
- Périmètres web « non-maîtrisés » (services Cloud, sites hébergés par des tiers)
- Périmètres « inconnus » d’Internet (forums, sites non indexés, deepweb)
- Monitoring :
- Alertes quotidiennes et qualifiées
- Synthèses managériales personnalisées (choix des indicateurs, répartition des alertes, évolution des tickets traités etc.)
- Facilité de déploiement :
- Aucune collecte de logs
- Implémentation d’agent
- Sonde au sein du SI nécessaire
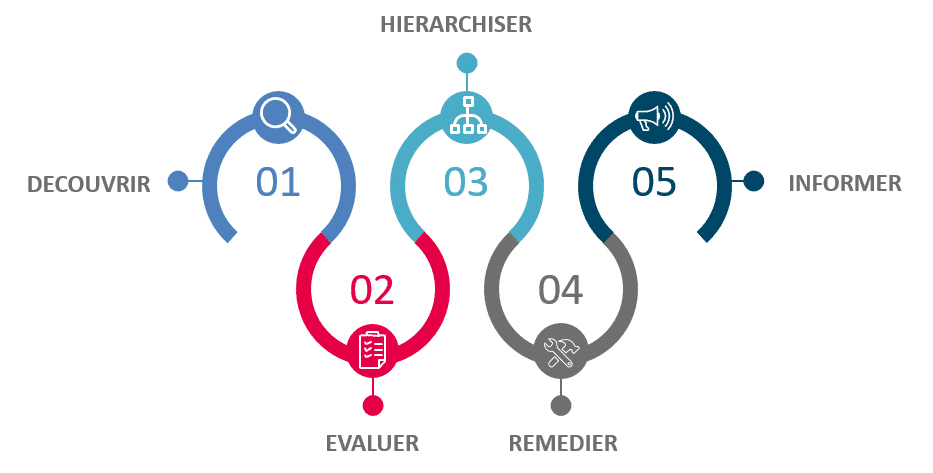
Audits de vulnérabilité
Qualys est un service cloud qui permet de fournir une visibilité immédiate et globale sur les points de vulnérabilité de vos systèmes informatiques et ainsi vous en protéger. Grâce à ce service, identifiez les menaces et surveillez les changements non planifiés qui se produisent sur votre réseau avant qu’ils ne se transforment en failles :
- Solution évolutive qui fournit une couverture de sécurité exhaustive à tous les réseaux et équipements (réseau interne, sites distants ou mobiles, environnements virtuels élastiques)
- Faible impact sur les équipes IT en termes de déploiement, de gestion et d’utilisation
- Résultats précis et hiérarchisés
- Scan hebdomadaires automatisés
- Supervision continue
- Facilité de déploiement :
- Aucun logiciel à installer ou à maintenir
- Accessibilité immédiate depuis un navigateur Web
- Évolutivité à l’échelle globale à la demande et déploiement depuis un cloud public ou privé
- Scan continu, identification et hiérarchisation des vulnérabilités :
- Cartographie du réseau
- Mises à jour quotidiennes et automatisées de la base de connaissances des vulnérabilités
- Exhaustivité des informations remontées : description de la vulnérabilité, conséquence et solution détaillée
- Gestion des actions correctives : génération et vérification automatiques des tickets d’incident, analyse des tendances des tickets d’incident et rapports, instructions simples pour éliminer les risques
- Reporting intuitif et complet :
- Tableau de bord pour la Direction avec synthèse de l’état de la sécurité globale et accès instantané aux détails de remédiation
- Rapports graphiques et tendanciels destinés aux responsables
- Rapports détaillés avec actions de remédiation vérifiées à l’attention des techniciens
- Solution dans le cloud actualisée en permanence : améliorations automatiques des fonctionnalités en toute transparence pour l’utilisateur
- Intégration à d’autres systèmes via API permettant notamment une intégration directe aux systèmes de génération de tickets d’incident et aux solutions de Help Desk
- Chiffrement de bout en bout et puissants contrôles d’accès à base de profils pour garantir la confidentialité de vos données de sécurité
Détection et protection des attaques DDoS
cegedim.cloud intègre dans Elastic Secured Endpoint une solution de détection et de protection contre les attaques DDoS, y compris de très grande capacité, avant qu’elles n’atteignent votre réseau. Ce service fournit une protection sur plusieurs couches (L3–L7), avec des technologies de balayage du cloud permettant de détecter, d’identifier et de prévenir les menaces en temps réel, tout en acheminant le trafic légitime vers votre site. La solution entièrement managée est déployée et gérée par nos experts sécurité.
Protection multi couches L3-L7
Protection contre les attaques DNS
Protection contre les attaques volumétriques
Acheminement du trafic légitime
Détection et protection des attaques DDoS
cegedim.cloud intègre dans Elastic Secured Endpoint une solution de détection et de protection contre les attaques DDoS, y compris de très grande capacité, avant qu’elles n’atteignent votre réseau. Ce service fournit une protection sur plusieurs couches (L3–L7), avec des technologies de balayage du cloud permettant de détecter, d’identifier et de prévenir les menaces en temps réel, tout en acheminant le trafic légitime vers votre site. La solution entièrement managée est déployée et gérée par nos experts sécurité.
- Protégez-vous contre les proxys d’hameçonnage, les proxys anonymes, les botnets, etc.
- Optimisez l’expérience utilisateur en leur permettant de rester en ligne pendant une attaque et minimisez ainsi tout impact sur vos utilisateurs
- Bénéficiez d’une visibilité et d’une compréhension profonde des attaques
Besoin d'informations supplémentaires sur les offres cegedim.cloud ?
Vous souhaitez en savoir plus sur les offres cegedim.cloud : N’hésitez pas à nous écrire, un expert vous contactera dans les plus brefs délais.